Your AWS environment looks perfect, pipelines are smooth, apps are deployed, S3 data is secure, IAM users are organized. Everything seems fine… until one morning your security team notices unusual API activity in CloudTrail.
Someone is inside your AWS account.
You did everything right or at least you thought so.
So how did it happen?
The truth: Over 90% of AWS security breaches are caused by misconfigurations, not AWS infrastructure flaws. Hackers exploit small mistakes that cascade into total compromise.
In this post, I’ll break down the most common AWS vulnerabilities exploited by attackers, how real pentesters discover them, modern attack chains, and how to defend your environment before it’s too late.
Why AWS Security Is Harder Than It Looks
AWS offers world-class infrastructure security but responsibility is shared.
Under the Shared Responsibility Model, AWS secures the cloud (hardware, virtualization, and managed services), but you are responsible for securing what you put in the cloud, your configurations, IAM policies, applications, and data.
Here’s where most breaches begin:
- Misconfigured resources (S3, EC2, Lambda)
- Over-privileged IAM roles
- Exposed credentials or tokens
- Weak network segmentation
- Insecure CI/CD or secrets management
- Lack of continuous monitoring
Attackers know these patterns and they automate scanning for them daily.
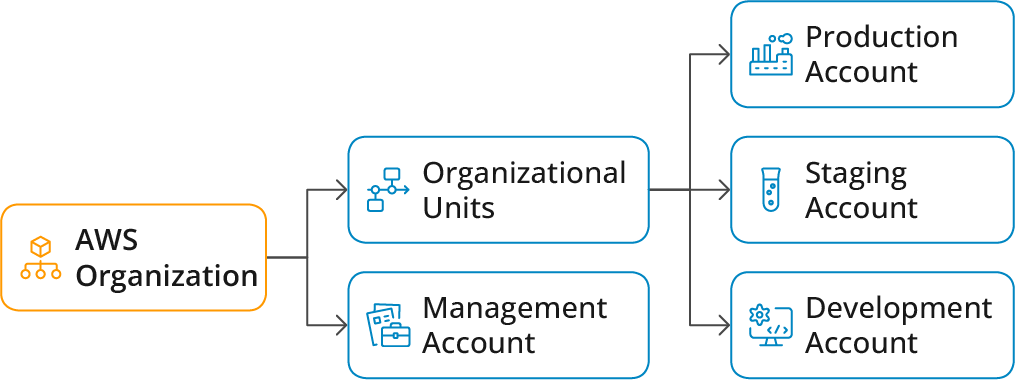
Pre-Engagement Rules and Scoping
Key Scoping Considerations:
- Account boundaries: Define which AWS accounts are in scope (production, staging, dev)
- Regional scope: Specify AWS regions (us-east-1, eu-west-1, etc.)
- Service scope: List specific services (EC2, S3, Lambda, RDS, etc.)
- Network ranges: Document CIDR blocks and VPCs in scope
- Credentials: Define what level of access testing will begin with (black box, gray box, white box)
- Time windows: Specify testing hours and duration
- Emergency contacts: Maintain a contact list for incident escalation
Testing Approaches:
- Black Box: External attacker perspective, no credentials provided
- Gray Box: Limited credentials (e.g., low-privilege IAM user)
- White Box: Full architectural documentation and admin access for comprehensive testing
Understanding AWS Architecture
AWS resources follow a hierarchical organization model:
Each AWS Account contains:
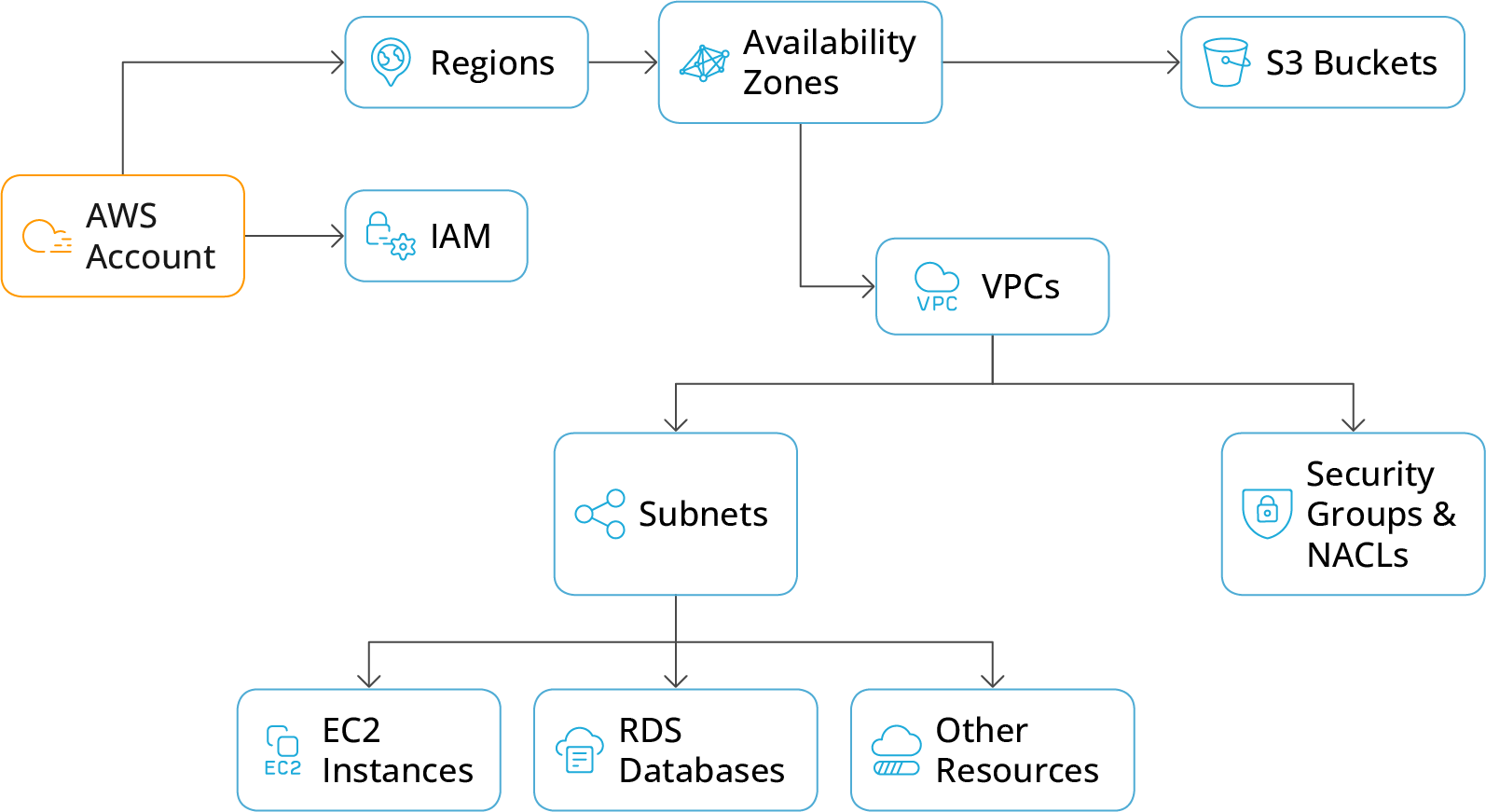
Key Security Services:
- IAM: Controls authentication and authorization
- CloudTrail: Logs all API calls for auditing
- GuardDuty: Threat detection service
- Security Hub: Centralized security findings
- Config: Tracks resource configurations and compliance
1. Misconfigured S3 Buckets: The Eternal Data Leak
The threat:
Amazon S3 is the backbone of AWS storage, but when configured incorrectly, it becomes a hacker’s goldmine. A single public bucket can expose terabytes of data in minutes.
Common mistakes:
- Buckets made public for testing and never reverted.
- “Everyone” or “AuthenticatedUsers” granted READ or WRITE access.
- Unencrypted data stored without SSE-KMS.
How attackers exploit it:
- Tools like S3Scanner, GrayhatWarfare, or awscli with –no-sign-request enumerate public buckets.
- Once found, attackers can download, alter, or replace data.
Real-world cases:
- Facebook (2019): 540 million user records exposed due to a public bucket.
- Verizon (2017): 14 million customer logs leaked.
Prevention:
- Block public access at the account and bucket level.
“`
aws s3api put-public-access-block –bucket my-bucket \
–public-access-block-configuration BlockPublicAcls=true
“` - Enforce encryption using SSE-KMS.
- Enable AWS Config or Security Hub rules to detect public access.
- Audit using ScoutSuite or Prowler (open-source AWS security auditing tools).
2. Overly Permissive IAM Policies: The Hidden Backdoor
The threat:
IAM (Identity and Access Management) defines who can do what.
The biggest enemy? Convenience.
Admins often attach AdministratorAccess to speed up troubleshooting or testing and forget to remove it.
Common issues:
- Wildcards (“Action”: “*”) in policies.
- Service roles with excessive trust relationships.
- Unused IAM users with active keys.
Attacker techniques:
- Enumerate IAM policies via AWS CLI or tools like Pacu (enumerate_iam module).
- Search for privilege escalation paths using Cloudsplaining or IAM Vulnerable Paths (iam-vuln).
- Use compromised credentials to assume high-privilege roles.
Real-world case:
Capital One Breach (2019): A misconfigured IAM role allowed a former AWS engineer to access 100 million customer records. Total impact: $80 million fine + reputational loss.
Prevention:
- Apply the Principle of Least Privilege (PoLP).
- Use AWS IAM Access Analyzer to flag over-permissive roles.
- Enforce MFA and temporary credentials (STS).
- Rotate keys and disable long-term access keys.
3. Exposed AWS Credentials The Shortcut to Root Access
The threat:
A leaked AWS Access Key = Instant compromise.
Developers often hardcode credentials in:
- GitHub repositories
- CI/CD environment variables
- Docker images
- Slack or Jira attachments
- CloudFormation templates
Attacker techniques:
- Use TruffleHog, GitLeaks, or Shhgit to find leaked keys.
- Exploit GitHub Search Dorks like:
filename:.aws/credentials access_key_id - Test the key validity with AWS CLI or Pacu session importer.
Real-world cases:
- Uber (2016): Hardcoded AWS credentials led to the breach of 57 million users.
- Toyota (2022): Exposed credentials in GitHub for five years revealed customer data.
Prevention:
- Store secrets in AWS Secrets Manager or HashiCorp Vault.
- Rotate credentials automatically.
- Use GitHub Secret Scanning, GitGuardian, or Snyk to detect leaks.
- Enforce CloudTrail and GuardDuty alerts for suspicious access.
4. Open Security Groups The Hacker’s Entry Door
The threat:
Security Groups are AWS’s built-in firewalls for EC2, but default or careless rules can expose critical services like SSH or RDP to the entire world.
Attack tools:
- Nmap, Masscan, or Shodan to detect open ports.
- Brute-force SSH or RDP with Hydra or Crowbar.
- Exploit known service vulnerabilities (e.g., EternalBlue, CVE-2021-44228 Log4Shell).
Real-world example:
Tesla (2018): Hackers exploited an open Kubernetes dashboard and used Tesla’s AWS instances for crypto-mining.
Prevention:
- Restrict SSH access to your IP range:
“`
aws ec2 authorize-security-group-ingress \
–group-id sg-12345678 –protocol tcp –port 22 –cidr YOUR_IP/32
“` - Use AWS WAF, Shield, and GuardDuty.
- Segment workloads into private subnets using VPCs and NACLs.
- Automate scans with CloudMapper or Prowler.
5. Insecure Lambda Functions and Serverless Misconfigurations
The threat:
Serverless functions are often overlooked.
Attackers exploit:
- Hardcoded environment variables with secrets.
- Over-privileged Lambda execution roles.
- Unpatched dependencies in layers or ZIP packages.
Tools & techniques:
- Analyze permissions using LambdaGuard.
- Scan for vulnerable dependencies with OWASP Dependency-Check.
- Exploit misconfigurations via Pacu’s lambda_enum module.
Prevention:
- Follow the Principle of Least Privilege for Lambda execution roles.
- Use AWS CodeGuru and Amazon Inspector for code scanning.
- Store secrets in AWS Secrets Manager.
6. Insecure CI/CD Pipelines and Third-Party Integrations
The threat:
CI/CD pipelines (GitHub Actions, Jenkins, GitLab CI) often have AWS credentials stored in plaintext or with overly broad IAM roles.
Attacker focus areas:
- Stolen build tokens or runner environment variables.
- Privilege escalation via compromised service roles.
- Poisoned dependencies or supply-chain attacks.
Prevention:
- Use OIDC authentication instead of long-term keys.
- Rotate runner tokens automatically.
- Scan pipelines with Checkov, tfsec, and GitGuardian.
How Pentesters Detect AWS Weaknesses
A professional pentester approaches AWS differently from traditional networks.
Here’s a typical methodology:
| Phase | Objective | Common Tools |
|---|---|---|
| Reconnaissance | Enumerate S3, EC2, Lambda, IAM, API Gateway | S3Scanner, CloudMapper, Nmap |
| Privilege Escalation |
Find misconfigured IAM roles or policies |
Pacu, Cloudsplaining |
| Credential Discovery | Detect secrets in code or metadata | TruffleHog, Metasploit, AWS CLI |
| Persistence | Abuse IAM roles, backdoors, or hidden policies | Pacu persistence modules |
| Reporting | Deliver remediation advice | ScoutSuite, Security Hub findings |
Advanced AWS Security Strategy (2025)
Take your AWS defense to the next level:
- Adopt Zero Trust Architecture verifies every API call.
- Shift Left Security scan code and IaC before deploying.
- Use AWS-native tools GuardDuty, Inspector, Macie, Detective.
- Automate Continuous Auditing AWS Config + Security Hub.
- Run regular red team simulations using frameworks like Atomic Red Team.
- Educating teams security awareness reduces 80% of risks.
AWS Pentesting Rules (Know Before You Test)
AWS allows pentesting on your own resources (no approval required) but you must avoid attacks affecting shared infrastructure.
Official AWS Policy:
AWS Penetration Testing Guidelines
Useful Tools & Resources
| Category | Tools |
|---|---|
| Recon | AWS CLI, CloudMapper, S3Scanner, Shodan |
| IAM Audit |
Pacu, Cloudsplaining, IAM Access Analyzer |
| Secrets | TruffleHog, GitLeaks, GitGuardian |
| Infra Audit | Prowler, ScoutSuite, Security Hub |
| Serverless | LambdaGuard, OWASP Dependency-Check |
| IaC Security | Tfsec, Terrascan, Checkov |
| Monitoring | GuardDuty, CloudTrail, Config, Macie |
Recon / Enumeration
- AWS CLI: Official AWS command-line interface (docs & install).
https://aws.amazon.com/cli/ - CloudMapper: AWS visualization & reconnaissance tool (NCC Group fork / repo).
https://github.com/duo-labs/cloudmapper - S3Scanner: Public S3 bucket scanner (GitHub).
https://github.com/sa7mon/S3Scanner - Shodan: Search engine for internet-facing devices and assets.
https://www.shodan.io/
IAM & Policy Auditing
- Pacu: AWS exploitation/pentest framework (Rhino Security Labs).
https://github.com/RhinoSecurityLabs/pacu - Cloudsplaining: IAM policy auditing tool for privilege risk discovery (Salesforce).
https://github.com/salesforce/cloudsplaining - AWS IAM Access Analyzer: AWS managed service for analyzing resource policies.
https://docs.aws.amazon.com/IAM/latest/UserGuide/access-analyzer.html
Secrets / Leak Detection
- TruffleHog: Secret scanning tool for git repos and diffs.
https://github.com/trufflesecurity/trufflehog - GitLeaks: Fast, flexible Git secret scanner.
https://github.com/zricethezav/gitleaks - GitGuardian: Commercial secret detection & monitoring (also free OSS scanners).
https://www.gitguardian.com/ - Shhgit: Finds secrets in public GitHub/Bitbucket repos (research tool).
https://github.com/eth0izzle/shhgit
Infrastructure & Cloud Auditing
- Prowler: AWS security best practices assessment, auditing & hardening.
https://github.com/toniblyx/prowler - ScoutSuite: Multi-cloud security-auditing tool (NCC Group).
https://github.com/nccgroup/ScoutSuite - AWS Security Hub: AWS managed service that aggregates security findings.
https://aws.amazon.com/security-hub/
Network Security & Detection
- AWS GuardDuty: Threat detection service for AWS accounts & workloads.
https://aws.amazon.com/guardduty/ - Amazon Inspector: Automated security assessment service for EC2 & container images.
https://aws.amazon.com/inspector/ - VPC Flow Logs: Network flow logging for VPCs (AWS docs).
https://docs.aws.amazon.com/vpc/latest/userguide/flow-logs.html
Serverless Security
- LambdaGuard: Lambda configuration & permission auditing (community tools vary).
https://github.com/DevonYeo/lambda_guard - OWASP Dependency-Check: Detect vulnerable dependencies in projects.
https://owasp.org/www-project-dependency-check/
IaC (Infrastructure-as-Code) Security
- Checkov: Static code analysis for Terraform, CloudFormation, Kubernetes, etc.
https://www.checkov.io/ - tfsec: Terrascan-like static analysis for Terraform.
https://github.com/aquasecurity/tfsec - Terrascan: Open source IaC security scanner (Accurics).
https://github.com/accurics/terrascan
Continuous Monitoring & Data Security
- AWS CloudTrail: API activity logging for AWS accounts.
https://aws.amazon.com/cloudtrail/ - Amazon Macie: Data loss prevention & sensitive data discovery for S3.
https://aws.amazon.com/macie/ - Amazon Detective: Visualize and investigate security findings.
https://aws.amazon.com/detective/
Pentest & Adversary Emulation Resources
- Atomic Red Team: Library of small, portable tests for emulating adversary techniques.
https://github.com/redcanaryco/atomic-red-team - MITRE ATT&CK: Knowledge base for adversary tactics and techniques.
https://attack.mitre.org/
Helpful Reading / Official AWS Guides
- AWS Penetration Testing Policy What AWS permits & prohibits for pentests.
https://aws.amazon.com/security/penetration-testing/ - AWS Security Best Practices (whitepaper) Official security guidance & best practices.
https://d1.awsstatic.com/whitepapers/Security/AWS_Security_Best_Practices.pdf

